Is this yet another GDPR article? Yes, but before you click on past, this article is a bit more specific, focussing on Event Organisers and a few important aspects relating to them.
Is this yet another GDPR article? Yes, but before you click on past, this article is a bit more specific, focussing on Event Organisers and a few important aspects relating to them.
If you have somehow managed to miss the basics here is a quick recap (otherwise skip the next two paragraphs). GDPR, the General Data Protection Regulation, comes into force on May 28th 2018 and is as dull as the name suggests but that doesn’t mean it should be ignored. GDPR is, in effect, a beefier version of the Data Protection Act and there are some significant aspects which have changed.
First off, the fines if you are found to be breaching the regulations could be huge – up to 4% of annual worldwide turnover (up to €20 million). Secondly, the onus with GDPR is focussed much more on how and why, with supporting documentation – no more simply ticking a box to say you comply. Lastly, and perhaps most significantly, with GDPR there is much more appetite to enforce, along with more resources to audit.
Nearly all of the material currently circulating is focussed around the more obvious areas of customer, supplier and employee data; everything from email addresses to bank accounts and the harvesting of information from websites, social media and direct mail campaigns. This is all valid and needs to be considered seriously, however, for events there are some additional areas which could too easily be overlooked.
CCTV
CCTV is not necessarily something that initially comes to mind when it comes to GDPR but it is very much part of it. The holding and releasing of CCTV footage is already well controlled but the new regulations go much further requiring information on camera placement, field of view and reasoning for coverage needed, coupled with proof of deployment and signage. This is a significant uplift for events compared to the current approach and will need to be factored into planning and deployment from the start.
It is also important to note that ANPR (Automatic Number Plate Recognition), drone and body-worn cameras will all need to be assessed too.
In practical terms, we are now expecting all temporary CCTV installations at events to undergo an audit during the build phase documenting the camera locations and reasoning for those locations. Field of view into public areas external to the event is especially important.
Agreement on how long footage is held for, the release process and who can receive the footage will also need to be under much tighter control.
Public Internet Access
Many events allow public access to the internet on an event Wi-Fi network after a ‘splash page’ which may capture details such as an email address to be used after the event to send marketing information. In the future this information is more controlled and must use explicit ‘opt-in’ clauses before the email address can be used.
Even the logging of an IP address (the identifier used when a device connects to the network) coupled with the user information is governed by GDPR, however, this information is required to be stored under the Investigatory Powers Act 2016 (aka the Snoopers’ Charter) so the way it is stored and who has access to it is very important.
For events which offer public internet access the method of access and what information is captured and stored will need to be reviewed, with likely changes to the Terms & Conditions and opt-in statements.
Supplier & Volunteer Registration Systems
Employee and customer data is called out in nearly all GDPR overviews but it is important to remember that GDPR covers all data including anything recorded for suppliers and volunteers. Any system (paper or electronic) which stores personal information must be assessed including aspects such as what information is stored, where it is stored, how it is stored, how it is used, how the owner can remove it and who has access.
Visitor/Attendee Information
Any personally identifiable information gathered on attendees, such as an email address falls under the same regulations – this could be via initial ticket purchase, attendee registration or at the event itself. Particular attention must be paid to any direct marketing as the attendee must explicitly opt in to any future communications and have means to update or remove their information.
Many of these areas are likely to require a Data Protection Impact Assessment (DPIA), this is a new tool and process which must be used when new technology is used or when there is high risk to individuals.
The new regulations also broaden the scope of ‘personal information’ to cover just about everything from a name, email or social information through to genetic, economic and cultural information. The holding of this information has to be shown to have positive, clear consent from the individual using ‘plain English’ type agreements.
An individual must be given the ability to view and update information, and importantly has the right ‘to be forgotten’, which means complete removal from all systems.
These changes may initially look very onerous, however, a lot can be covered by a sensible review and improvements to existing processes. The important thing is not to ignore it – the changes are coming and a lack of preparation will not be a defence if you are found to be in breach.
For events we work on we will be working closely with organisers to assist and make sure all aspects are covered, providing templates and guidance wherever possible. If you would like to discuss any aspect of GDPR impact on your event then please contact us and we will be happy to help.




 In conjunction with Ace Plant & TCP we launched the Ecolite P+ at Showman’s 2009. The Ecolite P+ was a more eco-friendly tower light using metal halide discharge lamps coupled with CCTV, Wi-Fi and a PA system. The light was palletised so that more units could be transported on a trailer and had a generator which could run for several days on its internal fuel tank.
In conjunction with Ace Plant & TCP we launched the Ecolite P+ at Showman’s 2009. The Ecolite P+ was a more eco-friendly tower light using metal halide discharge lamps coupled with CCTV, Wi-Fi and a PA system. The light was palletised so that more units could be transported on a trailer and had a generator which could run for several days on its internal fuel tank.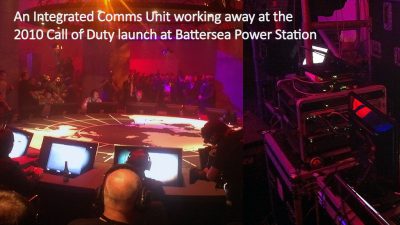
 The launch of Ka band satellite internet access in 2011 radically changed the use of satellite at events. Previously satellite internet was a relatively costly and difficult proposition which didn’t give a good user experience. The Ka band internet service was designed for broadband services, rather than broadcasters, using smaller dishes and allowing multiple users to share bandwidth to keep costs down. It has proved hugely popular and is now a common sight at events. It still suffers the important limitation of all satellite services – high latency – so can only be used for certain services and is a very different user experience to other types of connectivity.
The launch of Ka band satellite internet access in 2011 radically changed the use of satellite at events. Previously satellite internet was a relatively costly and difficult proposition which didn’t give a good user experience. The Ka band internet service was designed for broadband services, rather than broadcasters, using smaller dishes and allowing multiple users to share bandwidth to keep costs down. It has proved hugely popular and is now a common sight at events. It still suffers the important limitation of all satellite services – high latency – so can only be used for certain services and is a very different user experience to other types of connectivity. Since 2010 we had been working on RFID solutions with a crew catering system and later an accreditation/management system. In 2012 we worked with Intelligent Venue Solutions to bring a number of RFID related activities under one umbrella at a spin-out stand at Showmans.
Since 2010 we had been working on RFID solutions with a crew catering system and later an accreditation/management system. In 2012 we worked with Intelligent Venue Solutions to bring a number of RFID related activities under one umbrella at a spin-out stand at Showmans. In 2012 we introduced a people counting solution which we refined and extended into Live Event Footfall Analytics (LEFA) for Showman’s 2013. Structured counting, for example in well-contained routes such as exhibitions, is now well established, whereas unstructured crowd density analysis is still an evolving area but shows great potential longer term for helping manage crowd flows and density.
In 2012 we introduced a people counting solution which we refined and extended into Live Event Footfall Analytics (LEFA) for Showman’s 2013. Structured counting, for example in well-contained routes such as exhibitions, is now well established, whereas unstructured crowd density analysis is still an evolving area but shows great potential longer term for helping manage crowd flows and density. With more and more technology being deployed at events the next logical step is the integration of technology and communication between all aspects providing a rich level of event intelligence. From HD-CCTV, ticket scanning information and device location information, through to geo-tagged social media posts, a picture can be built up of what is happening on site and fed live into event control.
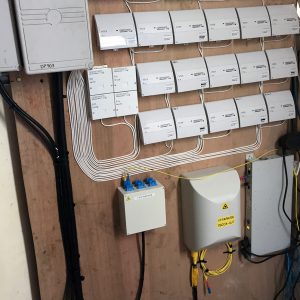
With more and more technology being deployed at events the next logical step is the integration of technology and communication between all aspects providing a rich level of event intelligence. From HD-CCTV, ticket scanning information and device location information, through to geo-tagged social media posts, a picture can be built up of what is happening on site and fed live into event control. Ever increasing requirements, demand for higher speeds and more capacity had driven a rise in the amount of fibre deployed around sites. Bigger sites were typically run with a fully routed design providing improved redundancy, increased speeds and better isolation between areas. This was often coupled with multiple gigabit internet connections which were diversely routed for redundancy.
Ever increasing requirements, demand for higher speeds and more capacity had driven a rise in the amount of fibre deployed around sites. Bigger sites were typically run with a fully routed design providing improved redundancy, increased speeds and better isolation between areas. This was often coupled with multiple gigabit internet connections which were diversely routed for redundancy. Extending on from the Intelligent Event additional components were demonstrated including Automated Number Plate Recognition (ANPR) and the Etherlive Monitoring Unit (EMU). The EMU is a type of IoT (Internet of Things) device which can be used to monitor a variety of things. It is particularly useful for monitoring power giving us early warning of power issues across a large event site.
Extending on from the Intelligent Event additional components were demonstrated including Automated Number Plate Recognition (ANPR) and the Etherlive Monitoring Unit (EMU). The EMU is a type of IoT (Internet of Things) device which can be used to monitor a variety of things. It is particularly useful for monitoring power giving us early warning of power issues across a large event site.
 e Oculus Rift, a project which has been exciting the technology community for some time, many argue that home virtual reality has finally arrived. Cheaper projects like Google Cardboard demonstrate that even those who do not want to splash out mega bucks can get themselves a piece of the action. Alongside full virtual reality there has also been an explosion in competitively priced 360 degree cameras bringing a much broader accessibility to a more immersive video experience.
e Oculus Rift, a project which has been exciting the technology community for some time, many argue that home virtual reality has finally arrived. Cheaper projects like Google Cardboard demonstrate that even those who do not want to splash out mega bucks can get themselves a piece of the action. Alongside full virtual reality there has also been an explosion in competitively priced 360 degree cameras bringing a much broader accessibility to a more immersive video experience. It may sound obvious but defining a clear specification for technical services means you’ll get what your event needs, when you want it at the right price.
It may sound obvious but defining a clear specification for technical services means you’ll get what your event needs, when you want it at the right price.